cybersecurity
-
Knowledge

What is identity theft?
តើអ្វីទៅជាជាការលួចយកអត្តសញ្ញាណ? ការលួចយកអត្តសញ្ញាណ គឺកើតមានឡើងនៅពេលដែល អ្នកលួច (ចោរ) ធ្វើការប្រមូលនូវព័ត៌មានផ្ទាល់ខ្លួនអ្នក ដូចជាលេខអត្តសញ្ញាណប័ណ្ណ, លេខសម្ងាត់, អាស័យដ្ឋាន, លេខគណនី ឬ PIN, ហើយប្រើប្រាស់នូវព័ត៌មានទាំងនេះ ដើម្បីបន្លំ ឬតាំងខ្លួនជាអ្នក។ ការលួចយកអត្តសញ្ញាណ ប្រើប្រាស់នូវទម្រង់ជា Phishing ឬកម្មវិធីមិនល្អ (malicious…
Read More » -
Knowledge

Poster – The Cybersecurity Lives of Millennials Infographic
ផ្ទាំងយល់ដឹងអំពីសន្តិសុខព័ត៌មាន – CyberSecurity ខាងក្រោមនេះគឺជាផ្ទាំងយល់ដឹងអំពីសន្តិសុខព័ត៌មាន ដែលត្រូវបានរៀបចំសម្រាប់ National Information Security Awareness Month នៅសហរដ្ឋអាមេរិក។
Read More » -
Awareness

NCSAM 2014 Launch
សូមទស្សនានូវវិដេអូឃ្លីប ដែលត្រូវបានថតនៅក្នុងព្រឹត្តិការណ៍ National Cyber Security Awareness Month 2014 នៅសហរដ្ឋអាមេរិក។ សូមទស្សនាទាំងអស់គ្នា ដើម្បីបានជាចំណេះដឹងទាំងអស់គ្នា!
Read More » -
Knowledge

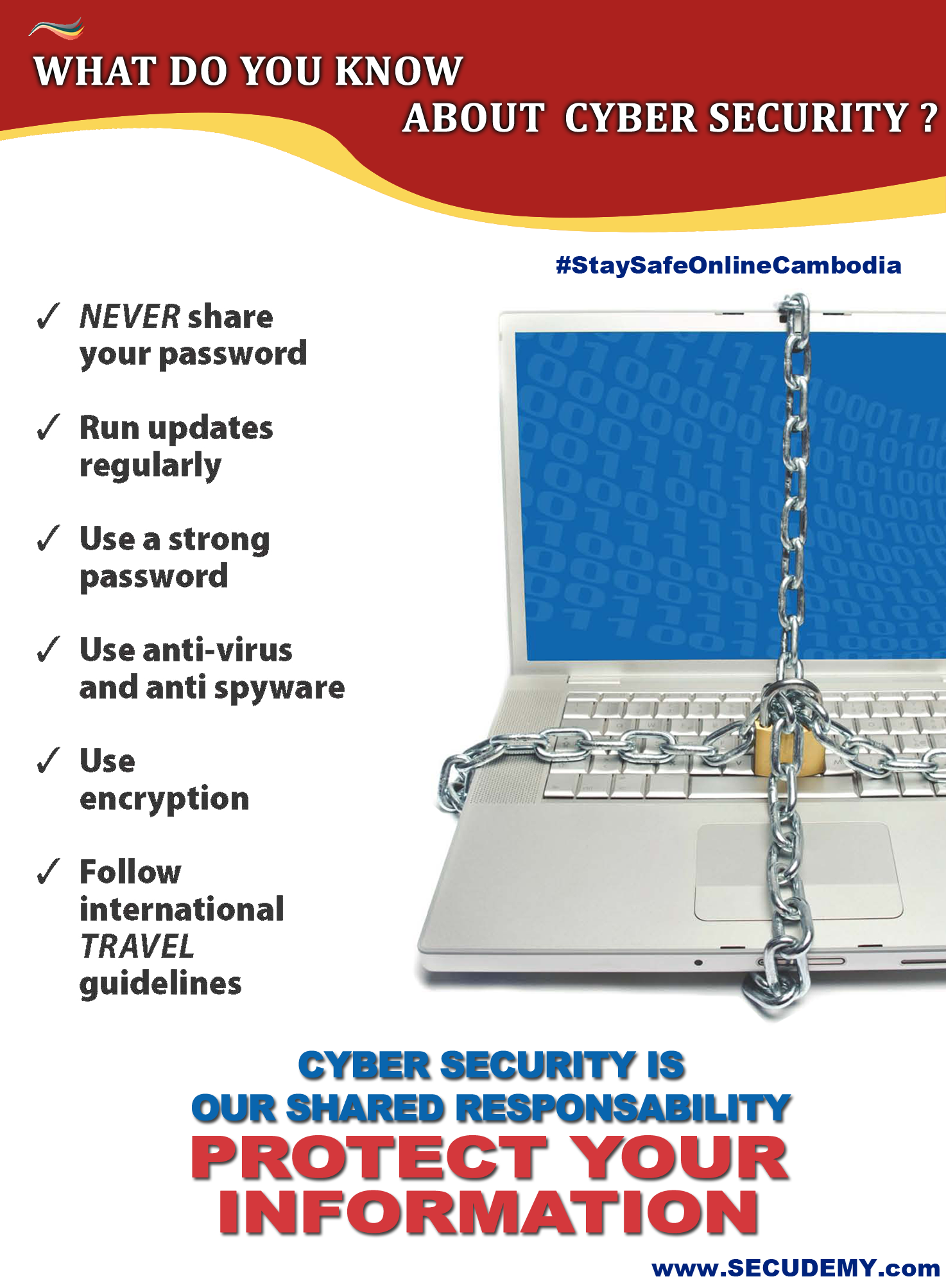
Poster – About CyberSecurity
ផ្ទាំងយល់ដឹងស្តីពីសន្តិសុខព័ត៌មាន – អ្វីខ្លះដែលអ្នកត្រូវដឹងអំពីសន្តិសុខអិុនធឺណេត សូមអរគុណទៅដល់និស្សិតនៃសាលកវិទ្យាល័យបៀលប្រាយ ដែលមានរាយឈ្មោះដូចខាងក្រោម ក្នុងការចូលរួមចំណែករចនាផ្ទាំងរូបភាព នៃការយល់ដឹងអំពីសន្តិសុខព័ត៌មាន ក្រោមប្រធានបទ “អ្វីខ្លះដែលអ្នកត្រូវដឹងអំពីសន្តិសុខអិុនធឺណេត” ក្នុងគោលបំណងធ្វើឲ្យការយល់ដឹងអំពីវិស័យសន្តិសុខព័ត៌មាននៅកម្ពុជា កាន់តែប្រសើរឡើង។ – Tin Kirivuth – Chi Kimneak – Sin Chanmony…
Read More » -
General

2020 – CyberSecurity by Trend Micro
២០២០ គឺជារឿងរាវមួយនាថ្ងៃអនាគតឆាប់ៗខាងមុខនេះ ដោយផ្អែកទៅលើរបាយការណ៍ ICSPA Project 2020។ ខ្សែវិដេអូខាងក្រោមនេះ គឺស្ថិតនៅក្នុង ទម្រង់មួយដែលបង្ហាញអំពីវិវឌ្ឍន៍នៃសង្គមនិងបច្ចេកវិទ្យានៅក្នុងសម័យកាលពិភពលោក ដែលបានរៀបរាប់ដោយគម្រោងខាងលើនេះ (ICSPA)។ អ្នកនឹងបាន ឃើញនូវវិធីសាស្ត្រដែលភាពជឿនលឿននៃឧបករណ៍ចល័ត និងបច្ចេកវិទ្យា Cloud មានឥទ្ធិពលទៅលើអ្វីដែលយើងមានសកម្មភាពជាមួយអ្នកផងផ្សេងទៀត និងពិភពលោក តើយើងធ្វើការយ៉ាងដូចម្តេចឯ ខាងក្រោមនេះគឺជាវិដេអូឃ្លីបចំនួន ៩វគ្គហើយដែលមានវគ្គនិមួយមានប្រមាណជា…
Read More » Wireless LAN Security Mega-Primer Part 9: Hotspot Attacks
In this video, we will look at hotspot based attacks. Most of us use public hotspots such as a Coffee…
Read More »Wireless LAN Security Mega-Primer Part 8: Hacking WLAN Authentication
In this video, we will learn how to hack through various WLAN Authentication schemas – Open and Shared Authentication. As…
Read More »How Do You Start Your Career in Cybersecurity?
The third of a three-part series titled “How to Get Hired in Cyber: Making the Cut at ManTech.’ Defense contractor…
Read More »Little Bets: How Breakthrough Ideas Emerge from Small Discoveries
Published on Mar 1, 2014 Sims demonstrates that the linear problem-solving we were conditioned to embrace, actively thwarts creativity. Rather, through…
Read More »Hugh Thompson and Guests
Published on Mar 1, 2014 Security guru and bestselling author Dr. Herbert “Hugh” Thompson has seen it all—hacked voting machines, exposed…
Read More »RSA 2014 Keynote – Scott Harrison, Charity : water
Published on Feb 28, 2014 Seven years ago Scott Harrison started charity: water with a mission to bring clean drinking water…
Read More »State of the Hack: One Year after the APT1 Report
Published on Feb 25, 2014 Nawaf Bitar Senior Vice President and General Manager, Security Business Unit, Juniper Networks, Inc. We are…
Read More »RSA 2014 Keynote – Philippe Courtot, Qualys
Published on Feb 28, 2014 Security professionals in general distrust the cloud—losing control, fly-by-night third party solutions, privacy and surveillance. However,…
Read More »Episode 9 – “Curiosity’s Claws” (End)
Welcome to Republic of South Sylvania. Mobile and cloud based technology influence every interaction citizens make. See what happens when…
Read More »Episode 8 – “Someone to Lynch”
“2020” is the story about the near future based on an ICSPA report entitled Project 2020. This video project takes…
Read More »