Video
Career Chat – Ethical Hacker
Confused about your career? gyaniguy has friendly advice from young people who are having fun doing unique stuff. Lloyd Rodrigues…
Read More »[Presentation] Data Protection and Compliance: Where Encryption Applies
Does your business face many industry and regulatory compliance mandates? Whether its PCI DSS, SOX, HPPA or FISMA, these regulations…
Read More »[Presentation] Why simple security is better security
Experts from IANS and Sophos explain why enterprise-class security offerings are a bad bet for smaller businesses, give tips on…
Read More »WIRELESS LAN SECURITY MEGAPRIMER PART 16: CAFFE LATTE ATTACK BASICS
Description: Welcome to Part 16 of the WLAN Security Megaprimer! Please start this series by watching Part 1http://www.securitytube.net/video/1756, if you have…
Read More »WIRELESS LAN SECURITY MEGAPRIMER PART 15: WEP CRACKING
Description: Welcome to Part 15 of the WLAN Security Megaprimer! Please start this series by watching Part 1http://www.securitytube.net/video/1756, if you have…
Read More »WIRELESS LAN SECURITY MEGAPRIMER PART 14: WEP IN-DEPTH
Description: Welcome to Part 14 of the WLAN Security Megaprimer! Please start this series by watching Part 1http://www.securitytube.net/video/1756, if you have…
Read More »EXPLOIT RESEARCH MEGAPRIMER PART 5 FREESSHD BUFFER OVERFLOW
Description: Welcome to Part 5 of the Exploit Research Megaprimer. Please begin this series by watching Part 1, if you have…
Read More »EXPLOIT RESEARCH MEGAPRIMER PART 3 STRCPY BUFFER OVERFLOW
Welcome to Part 3 of the Exploit Research Megaprimer. Please begin this series by watching Part 1, if you have not…
Read More »EXPLOIT RESEARCH MEGAPRIMER PART 2 MEMCPY BUFFER OVERFLOW
Welcome to Part 2 of the Exploit Research Megaprimer. Please begin this series by watching Part 1, if you have not…
Read More »Exploit Research Megaprimer Part 1 Topic Introduction by Vivek
We are starting a new Exploit Research Megaprimer on SecurityTube. The prerequisites for this series include the following: 1. Assembly Language…
Read More »Custom Wireless Regulation Database
Description: Sorry about the audio I know its out be a little and I sound like crap but Linux and my…
Read More »WIRELESS LAN SECURITY MEGAPRIMER PART 13 : SSL Man-In-The-Middle Attack
Description: Welcome to Part 13 of the WLAN Security Megaprimer! Please start this series by watching Part 1http://www.securitytube.net/video/1756, if you have…
Read More »-

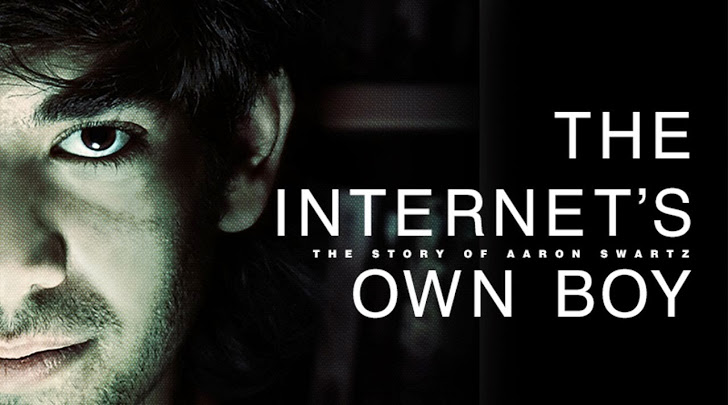
The Internet’s Own Boy – The story of Aaron Swartz
ភាពយន្ត Internet’s Own Boy – រឿងរ៉ាវរបស់ Aaron Swartz Aaron Hillel Swartz គឺជាអ្នកសរសេរកម្មវិធីកុំព្យួទ័រ សកម្មជនអិុនធឺែណត ជាសហស្ថានិកវិបសាយដ៏ល្បី Reddit ស្ថានិកអង្គការ Demand Progress និងជាសកម្មជនដែលជួយជ្រោមជ្រែងក្នុងការបង្កើតនូវ RSS…
Read More » BSIDESLA 2013 – Popping the Penguin: AN INTRODUCTION TO THE PRINCIPLES OF LINUX PERSISTENCE – MARK KITA
Description: Breaking in is half the battle. I’ve talked to so many people whose only objective is to try and break…
Read More »NOTACON 11 – A BRIEF INTRODUCTION TO GAME THEORY
Description: SynopsisFrom game shows to warfare, strategic decision-making surrounds us every day, whether you realize it or not. Game theory is…
Read More »